Curriculum
- 4 Sections
- 8 Lessons
- 12 Hours
- Basics of Network Security for SMEs and its importance in digital era3
- Possible risks and recommendations on mitigating risks related with Network Security3
- Integrating Network security cautions to Business Plans and Frameworks3
- Further Readings2
Curriculum
Fundamentals and Theoretical Basis
Network Security
Network security is a crucial activity that safeguards the integrity and usability of a network and data, encompassing both hardware and software technologies. It is also crucial for Small and Medium-sized Enterprises (SMEs) as they increasingly rely on interconnected technologies and online platforms.
Indeed, it involves multiple layers of defences, implementing policies and controls to restrict access to network resources and prevent malicious actors from exploiting them. It also involves practices, policies, and technologies designed to protect data, systems, and infrastructure from unauthorized access, attacks, and disruptions. This is particularly important in today’s digital world, where digitization has transformed our lives, work, and learning. Network security not only protects proprietary information but also safeguards an organization’s reputation.
Network security is the protection against failure, misuse, destruction, modification, unauthorized access, etc. of the network infrastructure. It allows you to take preventive measures to help protect against such situations. While you upload your data to the internet and think it is safe, hackers can breach that data, leak confidential information, or cause financial damage. Therefore, you need to secure your network. Network security is an important part of cybersecurity. It helps protect your network and the data stored within it from breaches, software and hardware intrusions, and more. Network security; It can be defined as a set of important rules, regulations and configurations based on threats, network usage, accessibility and complete threat security.
Types of Network Topology
There are several ways in which distinct components of a computer network might be joined to one another. The structure and connections between these elements are defined by the network topology. Before delving into network security, examples of network topologies that can be used in SMEs can be given as follows. The arrangement of a network that comprises nodes and connecting lines via sender and receiver is referred to as Network Topology.
The various network topologies are:
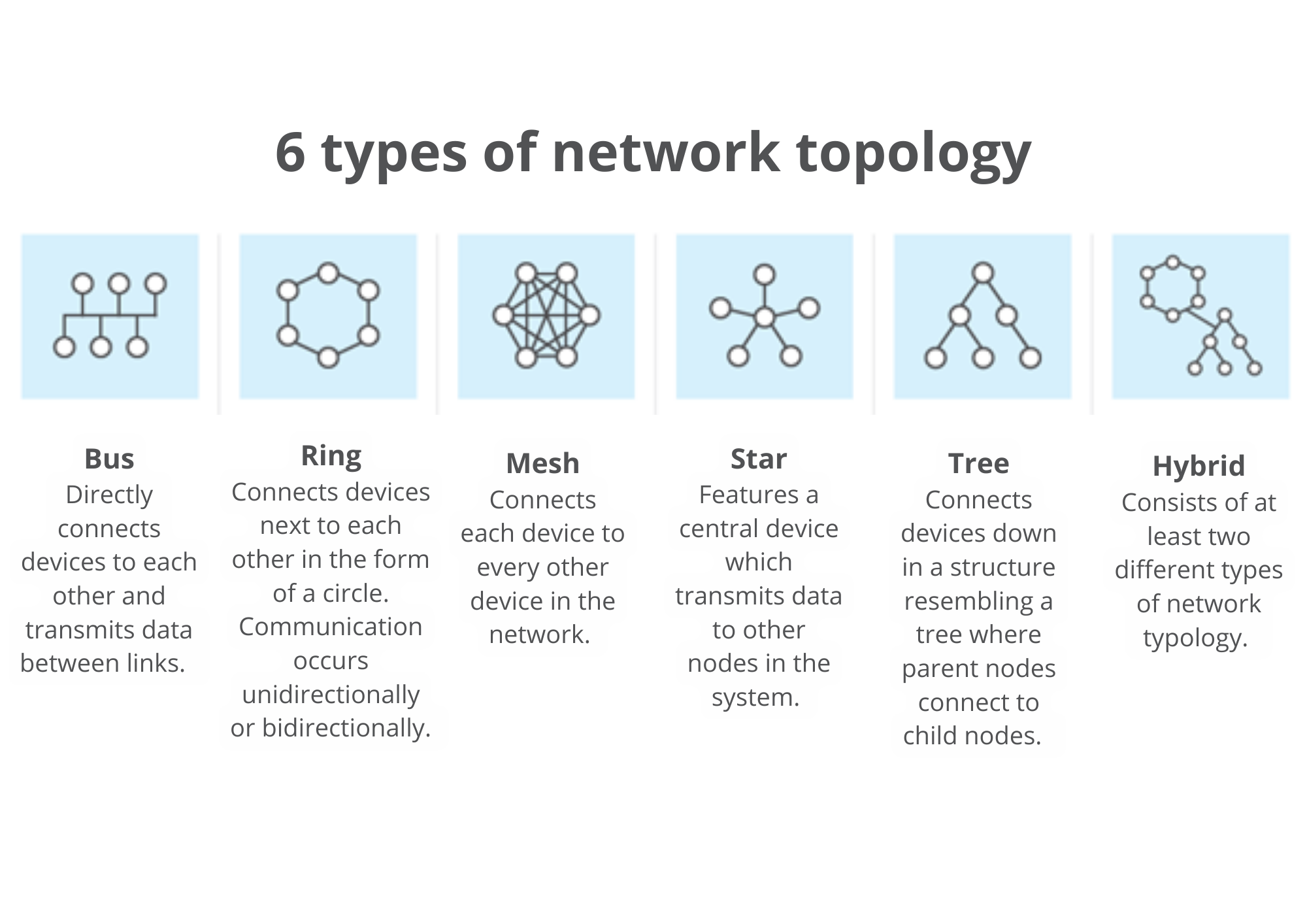
- Mesh Topology: In a mesh topology, every device is connected to another device via a particular channel.
- Star Topology: In Star Topology, all the devices are connected to a single hub through a cable.
- Bus Topology: A network type known as bus topology connects each computer and network device to a single wire.
- Ring Topology: It creates a ring in a ring topology, joining devices that have precisely two neighbours.
- Tree Topology: The Star topology is modified in this topology. The data flow in this architecture is hierarchical.
- Hybrid Topology: This topological technology is the combination of all the various types of topologies we have studied above.
In terms of performance, scalability, dependability, and security, every topology has pros and cons.
A star topology, for instance, is simple to set up and maintain, but it depends on a single device that may fail. Although a mesh topology is strong and secure, it might be more expensive and complex because it needs more connections and devices. Selecting a topology type that aligns with your network’s objectives and requirements is recommended. A secure network topology uses switches, routers, and firewalls to fortify the network perimeter, reducing the possibility of cyberattacks, illegal access, and data breaches.
ISO/IEC 27001 is the world’s best-known standard for information security management systems (ISMS). It defines the requirements an ISMS must meet. The ISO/IEC 27001 standard provides companies of any size and from all sectors of activity with guidance for establishing, implementing, maintaining and continually improving an information security management system. Regarding network security, there are 14 “domains” listed in Annex A of ISO 27001. The framework provided encompasses a comprehensive approach to information security within an organization, spanning various critical processes. The framework covers a comprehensive approach to information security within an organization, addressing key processes from the formulation of information security policies and the organization’s structure to human resources security and asset management.
Access control and the use of cryptography play vital roles in protecting sensitive information, while physical and environmental security is highlighted. It focuses on operational security, ensuring day-to-day processes align with security objectives. The framework extends to communications security, secure systems acquisition and development, and the management of supplier relationships. It also addresses information security incident management and its integration with business continuity. Together, these processes create a comprehensive strategy for enhancing an organization’s resilience against potential security threats.
It is also worth mentioning that ISO/IEC 27033-1:2015 provides an overview of network security and related definitions. It defines and describes the concepts associated with, and provides management guidance on, network security. (Network security applies to the security of devices, security of management activities related to the devices, applications/services, and end-users, in addition to the security of the information being transferred across the communication links.)
It is relevant to anyone involved in owning, operating or using a network. This includes senior managers and other non-technical managers or users, in addition to managers and administrators who have specific responsibilities for information security and/or network security, and network operation, or who are responsible for an organization’s overall security program and security policy development. It is also relevant to anyone involved in the planning, design and implementation of the architectural aspects of network security.
 Strong password security, minimum trust policy, cryptography, and implementation of OS and application patches should be ensured to reduce access attacks. A surprising number of access attacks are carried out through simple password guessing or brute force attacks against passwords.
Strong password security, minimum trust policy, cryptography, and implementation of OS and application patches should be ensured to reduce access attacks. A surprising number of access attacks are carried out through simple password guessing or brute force attacks against passwords.
To defend against this, a strong authentication policy should be created and implemented. Using strong passwords is crucial for safeguarding network devices. Here are the recommended guidelines to follow:
- Utilize a password that is at least 8 characters long, preferably 10 or more, for enhanced security.
- Make passwords complex by incorporating a mix of uppercase and lowercase letters, numbers, symbols, and spaces if allowed.
- Avoid easily identifiable information, such as common dictionary words, letter or number sequences, usernames, relatives’ or pets’ names, birthdates, ID numbers, ancestral names, or other easily recognizable biographical details.
- Intentionally misspell a password, for instance, Smith = Smyth = 5mYth or Security = 5ecur1ty.
- Change passwords regularly to limit the window of opportunity for threat actors in case a password is compromised.
- Refrain from writing passwords down or leaving them visible in prominent locations like desks or monitors.
A strategy for creating a strong password is to use the space bar and form a passphrase consisting of multiple words. This is known as a passphrase, which is often easier to remember than a simple password and is typically longer and more challenging to guess.
Cybersecurity Architecture: Five Principles to Follow (and One to Avoid)
Website Security
Website security is more important than ever while businesses are inclined towards digitalisation. Web servers, which host the data and other content available to your customers on the Internet, are often the most targeted and attacked components of a company’s network. Cybercriminals are constantly looking for improperly secured websites to attack, while many customers say website security is a top consideration when they choose to shop online. As a result, it is essential to secure servers and the network infrastructure that supports them. The consequences of a security breach are great: loss of revenues, damage to credibility, legal liability and loss of customer trust.
SMEs can take several measures to enhance website security and safeguard sensitive information. Firstly, implementing robust and up-to-date cybersecurity measures, such as firewalls and intrusion detection systems, is essential. Regularly updating and patching website software and applications helps address vulnerabilities and potential exploits. Utilizing secure and encrypted connections (HTTPS) is crucial for protecting data during transmission. In addition, enforcing strong authentication mechanisms, including multifactor authentication, adds an extra layer of defence against unauthorized access. Conducting regular security audits and vulnerability assessments aids in identifying and mitigating potential threats. Educating employees on cybersecurity best practices and promoting a culture of security awareness within the organization is also vital. Finally, establishing a contingency plan for incident response and regularly backing up website data ensures quick recovery in the event of a security breach. By adopting a comprehensive approach to website security, SMEs can significantly reduce the risk of cyber threats and fortify their online presence.