Curriculum
- 4 Sections
- 8 Lessons
- 12 Hours
- Basics of Network Security for SMEs and its importance in digital era3
- Possible risks and recommendations on mitigating risks related with Network Security3
- Integrating Network security cautions to Business Plans and Frameworks3
- Further Readings2
Curriculum
Fundamentals & Theoretical Basis
To secure your company’s network, you must identify all connected devices and devices on the network; establish boundaries between your systems and those of other parties; and enforce controls to make sure that events of denial-of-service, unauthorised access, or misuse can be prevented or, in the event that they do occur, quickly contained and recovered from.
Robust firewalls and intrusion detection/prevention systems are essential for SMEs to reduce the risk of unauthorized access, malware infections, and other cyber threats. Encryption protocols are crucial for transmitting sensitive data over the internet, especially for financial transactions and client information. Regular software updates and patch management are essential to address vulnerabilities and minimize potential risks. Employee education and awareness are also crucial for SMEs’ network security posture. By investing in robust security measures, staying informed about emerging threats, and fostering a security-conscious culture, SMEs can build a resilient digital infrastructure that protects assets, fosters customer trust, and ensures sustainable growth in an increasingly interconnected business landscape.
Internet of Things
The Internet of Things (IoT) has emerged as a technological breakthrough on many levels, connecting devices and objects to enable seamless communication and data exchange. For SMB owners and managers, understanding IoT applications is important to know how they can transform your business. Currently, IoT is mostly used in various business sectors to increase operational efficiency, improve decision-making processes and deliver innovative solutions. Some of the major areas where IoT is widely used are manufacturing, logistics and supply chain, and energy management.
While IoT devices may seem harmless because they are so small or so fragile, there is a real risk because they are networked general-purpose computers that can be compromised by attackers and cause problems beyond IoT security. Even the simplest devices can be very dangerous when compromised over the Internet.
An end-to-end approach must be taken using the right IoT technologies and protocols to protect employees, customers, valuable operational technologies and business investments with enhanced security for IoT infrastructures. Experienced IoT cybersecurity companies recommend a three-pronged approach to protecting data, devices, and connections:
- – Secure provision of devices.
- – Ensuring the security of the connection between devices and the cloud.
- – Ensuring the security of data in the cloud during processing and storage.
Some of the different types of network security attacks are as follows:
Virus: It is a downloadable malicious file that, once opened by a user, begins replacing codes on the computer with its own set of codes. When it spreads, the system files on the computer become corrupted and this can cause the files of other computer systems on the network to become corrupted.
- The virus cannot work on its own, it must work by adhering to another program.
- The virus gains the permissions of the program it connects to.
- Viruses replicate themselves and infect new programs.
You may consider to use antivirus programs within your company, activating the firewall and always using safe web sites.
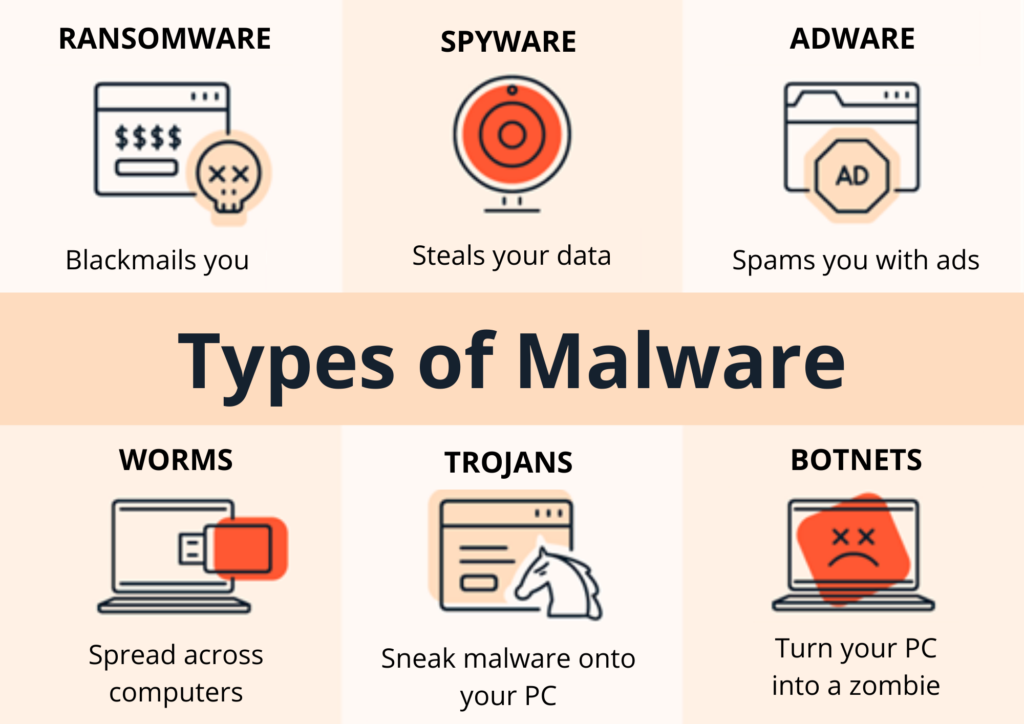
 Malware: It is among the most harmful and fast types of malicious attacks that help gain unauthorized access to a system or system network. Malware often self-replicates; that is, when one system is corrupted, malware easily corrupts all computer systems connected to the network over the internet. In case of malware, even an external device connected to the system can be corrupted. Keeping software updated, being cautious with emails, and regularly backing up your data are among the precautions you can take.
Malware: It is among the most harmful and fast types of malicious attacks that help gain unauthorized access to a system or system network. Malware often self-replicates; that is, when one system is corrupted, malware easily corrupts all computer systems connected to the network over the internet. In case of malware, even an external device connected to the system can be corrupted. Keeping software updated, being cautious with emails, and regularly backing up your data are among the precautions you can take.
Worm: It enters a certain system without the need for a user. If a user is running an application that is not very powerful, any hacker using the same internet connection can easily deliver malware to that application. Without the user’s knowledge, the application can accept and run this malware over the internet, resulting in the creation of a worm. Using network security tools, keeping pc systems updated, activating the firewall are among the precautions you can take.
Packet Sniffer: If a user places a passive receiver in a wireless transmitter zone, they see a copy of the transmitted packets. Often these packages contain confidential organizational data, trade secrets, etc. that can reach the package recipient. occurs. Cryptography is the best way to prevent such network security attacks.
Phishing: This is one of the most common forms of attacks on network security. Hackers send emails to users pretending to be from a known source, such as investors and bankers, creating a sense of urgency to attract users’ attention or excite them. There is a possibility that these emails contain malicious attachments or links that ask users to share confidential data.
Compromised Key: When a hacker obtains a network security key, they use a compromised key that acts as a tool to extract sensitive data and gain unauthorized access to secure data. This key consists of a code or number that helps interpret secure data without any notification to the sender or receiver.
Botnet: Malware that attacks a number of computers connected to each other over a private network. Hackers access and control all systems on that network without the owner’s knowledge. All computers in this network are called zombies, which disrupt a large number of devices according to the instructions of the hacker.
DoS: DoS is known as denial of service. This attack has the ability to partially or completely destroy users’ networks. DoS can also attack even a complete IT infrastructure, making it unusable for real users. There are also precautions to be taken to mitigate DoS Attacks: One of the first signs of a DoS attack is a large number of user complaints about unavailable resources or unusually slow network performance. A network exploitation software suite should be running at all times to minimize the number of attacks. Network behavior analysis can detect unusual usage patterns that indicate a DoS attack is occurring.
Security Protocols: Successful protocols that use public key-based encryption include PGP (Pretty Good Privacy), SSL (Secure Socket Layer) and SSH (Secure SHell), although they can often be used without requiring a certificate. These approaches are briefly explained below.
Malware: Difference Between Computer Viruses, Worms and Trojans
There are a few steps you need to take to ensure your company’s network security. You can define these steps in various ways in the Cyber Action Plan, we have some suggestions below.
1. Secure internal network and cloud services
Firewalls and web filtering proxies, together with other robust user authentication and policy enforcement technologies, should be used to keep your company’s network isolated from the public Internet. It is also advisable to use additional security and monitoring tools, including intrusion detection systems and antivirus software, to spot and prevent dangerous code and unwanted access attempts.
2. Develop strong password policies
Static passwords are not as secure as two-factor authentication techniques, which demand two different forms of verification that you are who you say you are. A personal security token that shows rotating passcodes to be used in addition to a password that has been set is one such example. Two-factor authentication, however, might not always be feasible or useful for your business. Password rules ought to motivate staff members to use the strongest passwords they can without encouraging them to write them down or use the same ones again. That entails creating long, complicated, and unpredictable passwords (at least ten characters), changing them frequently, and having people who know them strictly protect them.
3. Secure and encrypt your company’s Wi-Fi
A company may operate a Wireless Local Area Network (WLAN) for customers, guests, and visitors, but it should be separate from the main company network to prevent public network traffic from affecting internal systems. Internal, non-public WLAN access should be restricted to specific devices and users, and dual connections should be prohibited by technical controls on each capable device. All users should be given unique credentials with preset expiration dates for accessing the internal WLAN. Due to security flaws in older forms of wireless encryption, the company’s internal WLAN should only use Wi-Fi Protected Access 2 (WPA2) encryption.
4. Regularly update all applications
As fixes and firmware updates become available, all systems and software—including networking equipment—should be updated on a timely basis. When feasible, use automated updating services, particularly for security systems like intrusion prevention systems, web filtering tools, and anti-malware software.
5. Set safe web browsing rules
A well-liked and safe solution if your business has to let distant users access to its internal network over the Internet is to use a secure Virtual Private Network (VPN) system in conjunction with robust two-factor authentication, which can be accomplished using either hardware or software tokens.
6. Mitigating common network attacks
Continuous vigilance and training are required to defend the network against attacks. Employees should be trained and guided about the risks of social engineering and strategies should be developed to verify identities by phone, email, or in person.
Here are some of the best practices for securing a network:
- – Develop a detailed security policy for the company.
- – Physical access to systems should be controlled.
- – Sensitive data should be encrypted and password protected.
- – Backup should be made and backed up files should be tested regularly.
- – Unnecessary services and ports should be closed.
- – To prevent buffer overflows and privilege escalation attacks, patches should be updated weekly or daily if possible.
- – Security audits should be performed to test the network.
In addition to the aforementioned precautions, there are several other measures that can be implemented to bolster overall cybersecurity.
To enhance network security, organizations should establish secure web browsing rules, educate employees about potential threats, and create guidelines for the safe use of flash drives. This includes scanning external storage devices for malware before connecting them to company computers. Regular updates and maintenance of antivirus and antimalware software ensure resilience against evolving attacks. Employee training in security protocols, such as strong passwords, social engineering tactics, and vigilantness against potential threats, is also crucial. Regular workshops and awareness programs can empower staff to recognize and respond effectively to potential security risks.
By adopting this preventive approach, organizations can significantly enhance their cybersecurity posture and better protect their digital assets against a variety of potential threats.