Curriculum
- 4 Sections
- 15 Lessons
- 6 Hours
- Fundamentals of Secure Endpoint Protection: Importance and Components of Endpoint Security6
- Endpoint Security Management and Tools: Security, Identity, Access Management and Endpoint Detection and Response (EDR) Solutions6
- Future Approaches to Endpoint Security: Artificial Intelligence and Machine Learning, Cloud-Based Security, Training and Awareness Programs5
- Further Readings1
Curriculum
Endpoint Security Management Systems (EPMS)
Welcome to the specific subunit on “Endpoint Security Management and Tools: Security, Identity, Access Management and EDR Solutions”. This section is designed for SMEs to manage and protect all endpoints on their networks (computers, mobile devices, servers, etc.) from a central location. Here we will examine endpoint protection management systems, identity and access management and endpoint detection and response. By the end of this subunit, participants will understand the theoretical aspects of endpoint protection management systems and identity and access management and also gain hands-on experience in endpoint detection and response software.
Endpoint Security Management Systems (EPMS)
Endpoint Protection Management Systems (EPMS) are security solutions that allow businesses and organizations to manage and protect all endpoints (computers, mobile devices, servers, etc.) in their network from a centralized location. These systems perform a range of functions including protection against cyber threats, incident response, and reporting. The importance of EPMS becomes more evident when considering the increasing cyber threats and complex IT environments. These systems enable quick detection, response, and reporting of threats, strengthening an organization’s security posture and helping to minimize damage that could result from cyberattacks. The main functions and importance of EPMS software include Threat Prevention and Detection, Management Consoles and Centralized Management, Incident Response and Reporting, Updates and Patch Management, Application Control and Whitelisting, Configuration Management, Access Control, and Mobile Device Management.
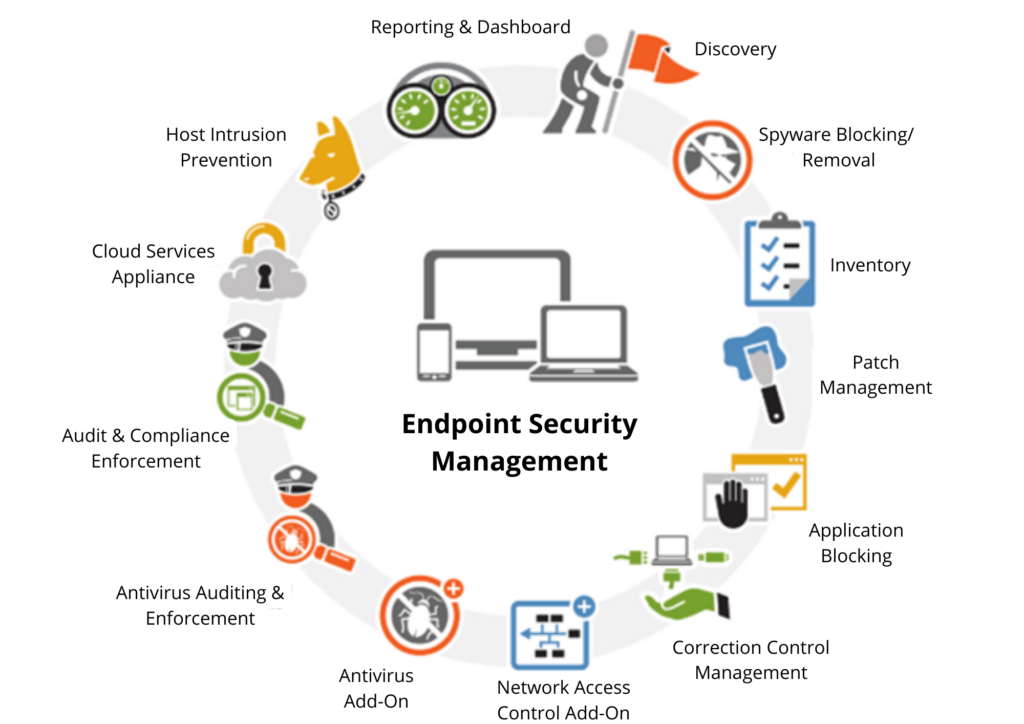
Figure 5
(Source: https://www.business-software.com/blog/byod-like-cancer-endpoint-security-cure/)