Curriculum
- 4 Sections
- 13 Lessons
- 6 Hours
Expand all sectionsCollapse all sections
- Incident Detection and Reporting5
- Incident Response and Mitigation Strategies5
- Post-Incident Review and Reporting5
- Further Readings1
Curriculum
Incident Analysis and Root Cause Identification
In this section, we delve into the initial steps following a security incident, focusing on understanding what happened and why.
- Detailed incident logging: The first step in effective incident analysis involves meticulously documenting every aspect of the incident. This includes the time of detection, how the breach was identified, the type of threat, affected systems, and the sequence of events. Detailed logging provides a comprehensive overview, essential for understanding the scope and impact of the incident.
- Evidence collection and preservation: Gathering and preserving digital evidence is crucial for root cause analysis. This process involves securing logs, system snapshots, and other relevant data before they are overwritten or corrupted. Proper evidence handling ensures the integrity of the investigation and aids in legal proceedings, if necessary.
- Root Cause Analysis (RCA): RCA is the process of identifying the underlying reasons for the incident. It involves examining why the incident occurred and how the threat actors gained access. Techniques such as the Five Whys, fault tree analysis, or fishbone diagrams can help in tracing back to the root cause. Understanding the root cause is crucial for developing effective mitigation strategies to prevent recurrence.
- Collaboration and communication: Incident analysis often requires collaboration between various organizational departments, such as IT, security, legal, and HR. Open communication and information sharing facilitate more accurate identification of the root cause and ensure a unified approach to address the underlying issues.
- Lessons learned and knowledge sharing: Once the root cause is identified, it’s important to share findings with relevant stakeholders. Lessons learned sessions help in disseminating knowledge gained from the incident and in implementing corrective measures across the organization. This step is vital for improving incident response strategies and cybersecurity measures.
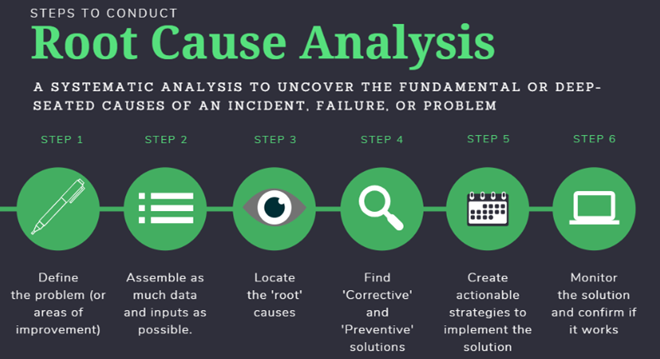
Figure- 7