Curriculum
- 4 Sections
- 13 Lessons
- 6 Hours
- Incident Detection and Reporting5
- Incident Response and Mitigation Strategies5
- Post-Incident Review and Reporting5
- Further Readings1
Curriculum
Proactive Approaches and Best Practices
Developing a proactive security culture: Security is not only a technological issue but also a matter of organizational culture. A proactive approach begins with raising security awareness among all employees and adopting the best security practices. Training programs, regular awareness sessions, and security simulations are essential to enable employees to recognize potential threats and respond appropriately.
Risk assessment and management: Organizations should continuously evaluate their assets, threat vectors, and vulnerabilities. Risk assessment processes help in the pre-emptive identification and prioritization of potential security incidents. This ensures that resources are focused on the most serious threats, enhancing the effectiveness of incident detection and response processes.
Integration of threat intelligence: Proactive incident detection requires ongoing monitoring and analysis of current threat intelligence. This information aids in understanding cyber threats and attack methodologies, helping organizations to keep their defence strategies updated. Integrating with external threat intelligence sources ensures that incident detection systems are more accurate and effective.
Developing and testing incident response plans: An effective incident response plan enables a quick and organized response to any security incident. The plan should clearly define roles, responsibilities, and communication protocols. Regular drills and simulations test the effectiveness of the plan and ensure teams are prepared for a real-life incident.
Continuous improvement: Security is a process, not a one-time activity. Organizations should continuously review and improve their incident detection and response processes. This is achieved through post-incident analyses, technology updates, and modifications in processes. Continuous improvement ensures that resilience against threats increases over time.
Adopting these proactive approaches and best practices helps organizations to be better prepared against cybersecurity threats and continually enhance their incident detection and response capabilities.
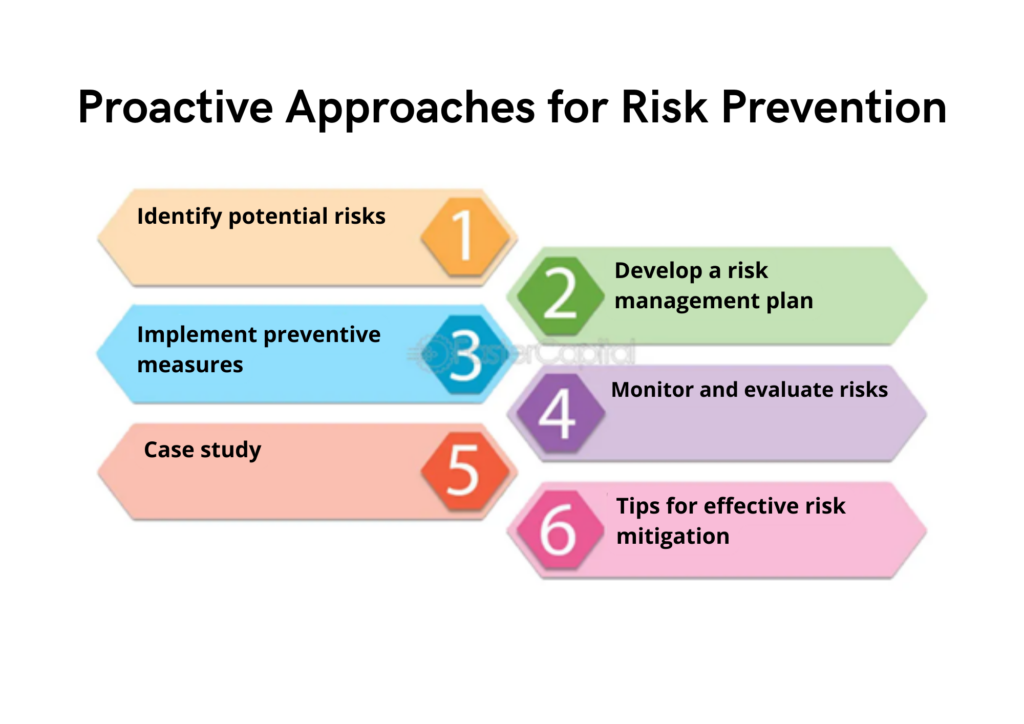
Figure-3
(Source: https://fastercapital.com/startup-topic/Proactive-Approaches.html)