Curriculum
- 4 Sections
- 7 Lessons
- 6 Hours
- Introduction To Secure Software Development: Understanding Secure Software Development3
- Secure Development Practices: Secure Coding Techniques, Threat Modelling and Risk Assessment3
- Implementation And Maintenance: Deployment of Secure Software and Post-Deployment Security Practices3
- Further Readings1
Curriculum
Fundamentals and Theoretical Basis
Secure Software Development: Understanding Secure Software Development
Welcome to the foundational subunit on Secure Endpoint Protection, a crucial aspect for all Small and Medium-sized Enterprises (SMEs) in today’s digital era. This section is dedicated to introducing you to the importance, basic concepts and principles of secure software development. In this module, software security concepts will be explained and the basic steps in the secure software development process will be emphasized. Additionally, by focusing on providing the knowledge and skills required for secure software development practice, participants will be encouraged to reduce security vulnerabilities and create software that is more resistant to cyber threats.
Understanding Secure Software Development
Secure software development is an approach to creating computer software that emphasizes the importance of considering security at every phase of the development process. It is a proactive and comprehensive strategy to prevent security vulnerabilities and threats from affecting software applications. Here’s a deeper look into the concept:
- – Key aspects of Secure Software Development: Security considerations are integrated from the earliest stages of design and architecture, rather than being an afterthought.
- – Risk analysis: Developers and security teams assess potential risks and threats to the software and its data. This helps in prioritizing security features and controls.
- – Secure coding practices: Developers follow coding standards and guidelines that help avoid common vulnerabilities such as SQL injection, cross-site scripting (XSS), and buffer overflows.
- – Code review and static analysis: Code is regularly reviewed by peers, and static analysis tools are used to scan for potential security issues.
- – Dynamic analysis and testing: Software undergoes dynamic analysis and security testing, including penetration testing, to identify and fix runtime vulnerabilities.
- – Dependency management: Third-party libraries and dependencies are kept up-to-date and checked for known vulnerabilities.
- – Incident response: A plan is in place for responding to security incidents, including patch management and communication strategies.
- –Education and training: Developers and relevant personnel are trained in secure coding practices and kept aware of the latest security threats.
Importance of Secure Software Development:
- Protecting Sensitive Data.
- Maintaining Trust.
- Regulatory Compliance.
- Reducing Costs.
- Avoiding Service Disruptions.
- Competitive Advantage.
- Preventing Legal Consequences.

Figure-1
(Source: https://integrio.net/blog/improving-software-security)
The significance of security in the software development lifecycle (SDLC)
Security in the Software Development Lifecycle (SDLC) is a critical aspect that demands attention at every stage of development. Integrating security into the SDLC ensures that the software is built with a strong defence against potential cyber threats, which are increasingly sophisticated and ever-changing. By prioritizing security from the beginning, developers can identify and mitigate vulnerabilities early, which is far more cost-effective than addressing these issues after the software has been deployed. Early detection not only saves money but also reduces the complexity of fixes and the risk of introducing new issues during remediation.
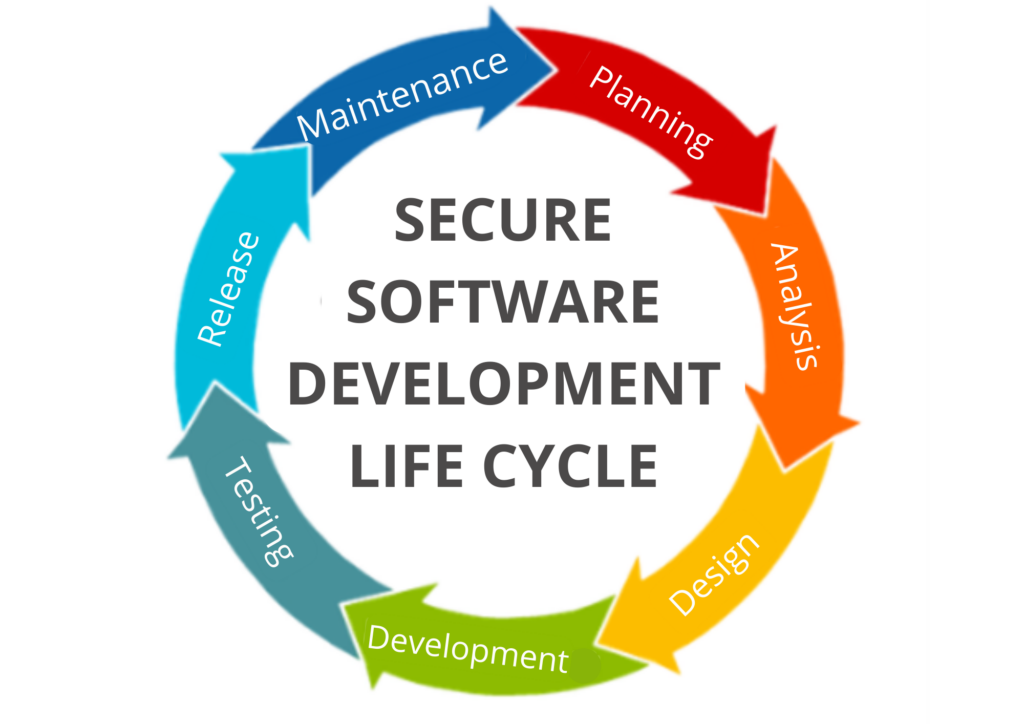
Figure 2
(Source: https://softprodigy.com/secure-software-development-life-cycle-navigate-your-way-to-security/)
Principles of Secure Development
Secure development is a critical aspect of modern software engineering that focuses on embedding security principles into every phase of the software development lifecycle (SDLC). By adhering to secure development principles, organizations can produce software that is resilient to cyber threats and capable of protecting user data and maintaining functionality even when under attack. Here are some of the core principles of secure development;
Proactive Security Integration: This involves considering security implications during the design phase, choosing secure frameworks and libraries, and ensuring that security requirements are defined alongside functional requirements.
Least Privilege: Software should operate with the minimum level of privileges necessary to accomplish its tasks. This principle limits the potential damage that can occur if the software is compromised. It applies not only to the software itself but also to the users and systems that interact with it.
Defence in Depth: No single security measure is foolproof, so employing multiple layers of security controls (physical, technical, administrative) can provide redundancy and mitigate the risk of a single point of failure.
Fail Securely: When software encounters an error, it should fail in a way that does not compromise security.
Security by Design: Security should be an integral part of the software design.
Regular Security Testing: Security testing should be an ongoing process, not just a one-time event before deployment.
Principle of Least Knowledge (POLK): Also known as the principle of least disclosure, this principle states that a system should not expose more information or functionality than is necessary for its intended purpose.
Secure Defaults: The default configuration settings of software should be secure out of the box, requiring users to opt into less secure configurations if they choose.
Open Design: The design of the software should be open to review by experts, as transparency can lead to more robust security solutions.
Input Validation and Sanitization: Validating and sanitizing inputs can prevent common attacks such as SQL injection, cross-site scripting (XSS), and others.
Patch Management: Keeping software up to date is crucial for security. A process should be in place to quickly apply patches and updates when vulnerabilities are discovered.
Incident Response and Recovery: Organizations must have plans in place for responding to security incidents.
Education and Awareness: All stakeholders, including developers, testers, and end-users, should be educated about the importance of security.
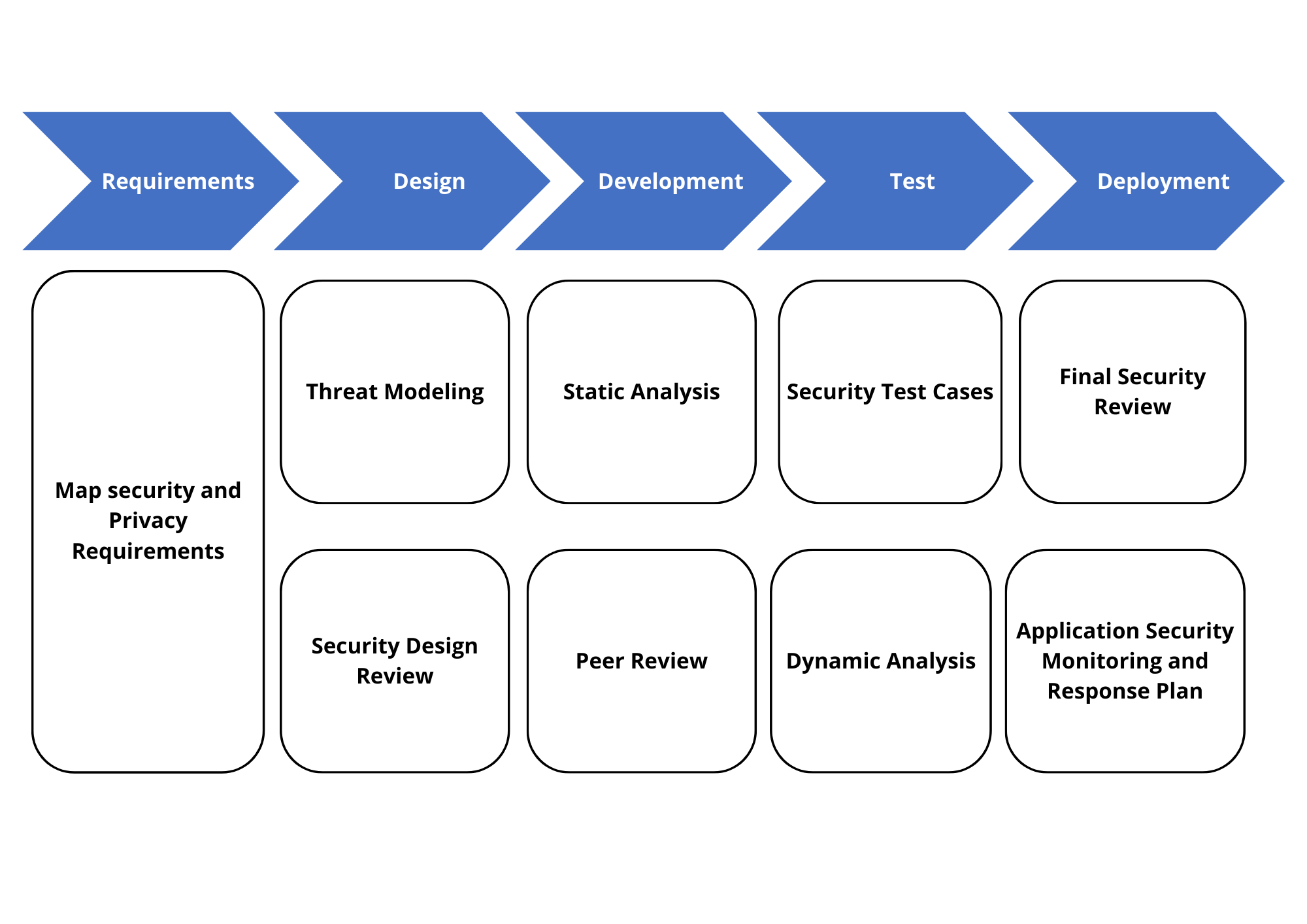
Figure-3
(Source: https://www.semanticscholar.org/paper/SECURE-SOFTWARE-DEVELOPMENT-FRAMEWORK-%3A-PRINCIPLES)