Curriculum
- 4 Sections
- 7 Lessons
- 6 Hours
- Introduction To Secure Software Development: Understanding Secure Software Development3
- Secure Development Practices: Secure Coding Techniques, Threat Modelling and Risk Assessment3
- Implementation And Maintenance: Deployment of Secure Software and Post-Deployment Security Practices3
- Further Readings1
Curriculum
Fundamentals and Theoretical Basis
Secure Coding Techniques
Secure coding techniques are essential for developers to create applications that are resistant to attacks and protect user data. These techniques are a subset of secure development practices that focus specifically on writing code in a way that guards against the introduction of security vulnerabilities. Here’s an overview of some key secure coding techniques;
- Input Validation: Ensure that all input received from users, files, databases, or any external source is validated for type, length, format, and range before using it in the application.
- Output Encoding: When displaying or transmitting data, encode it appropriately to prevent injection attacks, such as Cross-Site Scripting (XSS). For example, HTML output should be encoded to prevent the browser from executing malicious scripts.
- Parameterized Queries: Use parameterized queries or prepared statements when accessing databases to prevent SQL injection attacks.
- Least Privilege: Apply the principle of least privilege by running processes and accessing resources with the minimum permissions necessary.
- Authentication and Authorization: Implement strong authentication mechanisms and enforce strict authorization checks to ensure that only legitimate users can access sensitive functions and data.
- Password Management: Store passwords securely using strong, adaptive hashing algorithms such as bcrypt or Argon2.
- Session Management: Store session data securely and ensure that session tokens are transmitted securely, typically in HTTP headers with proper use of HTTPS.
- Error Handling: Implement robust error handling that does not expose sensitive information to the user.
- Encryption: Use encryption to protect data in transit (with TLS/SSL) and at rest. Ensure that encryption implementations are current and use strong algorithms and keys.
- Code Signing: Sign your code to ensure its integrity and origin. This helps prevent tampering and can alert users to unauthorized changes.
- Secure File Operations: When handling files, ensure that file operations are performed securely to prevent directory traversal attacks and ensure that file permissions are set appropriately.
- Memory Management: For languages that do not automatically manage memory, such as C and C++, be diligent about allocating, using, and freeing memory to prevent memory leaks and buffer overflows.
- Concurrency and Race Condition Handling: Write code that is safe for concurrent execution and handles race conditions to prevent issues like time-of-check to time-of-use (TOCTOU) bugs.
- Data Sanitization: Sanitize data that will be passed to interpreters or command shells to prevent injection attacks.
- Code Reviews and Static Analysis: Regularly conduct code reviews with a focus on security and employ static analysis tools to automatically detect potential vulnerabilities in code.
- Dependency Security: Keep third-party libraries and dependencies updated and check for known vulnerabilities using software composition analysis tools.
Figure-4
(Source: https://securityboulevard.com/2022/01/7-security-coding-guidelines-to-keep-in-mind/)
Threat Modelling and Risk Assessment
Threat modelling and risk assessment are proactive processes used in cybersecurity and software development to identify, prioritize, and mitigate potential threats to a system. These practices are part of a broader approach to security known as Security by Design, which emphasizes the importance of incorporating security measures from the earliest stages of development. Threat modelling is a structured approach to identifying and addressing potential threats to a system.
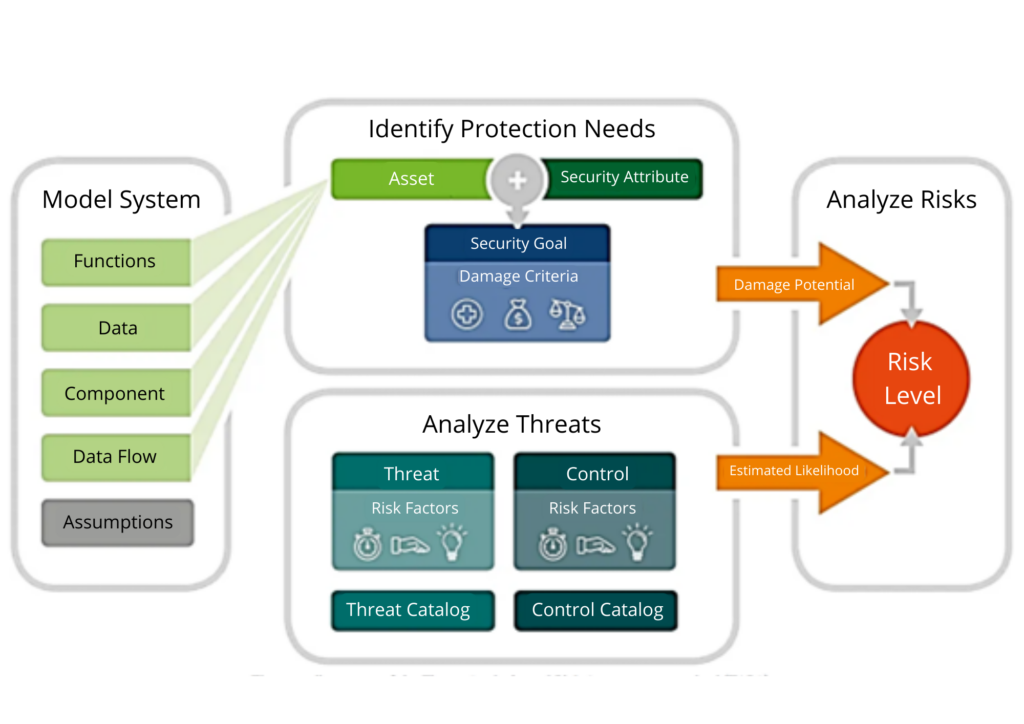
Figure-5
(Source: https://www.security-analyst.org/threat-analysis-and-risk-assessment/)
Best Practices for Threat Modelling and Risk Assessment
- Start early: Begin threat modelling and risk assessment in the design phase and iterate throughout the development lifecycle.
- Involve multidisciplinary teams: Include members with diverse perspectives, such as developers, security professionals, operations staff, and business analysts.
- Use standard frameworks and methodologies: Apply established frameworks (like NIST, ISO, or OCTAVE) and methodologies (like STRIDE or PASTA) to guide the process.
- Keep documentation up to date: Ensure that all findings and actions are well-documented and easily accessible.
- Integrate with the development process: Embed threat modelling and risk assessment into the software development lifecycle (SDLC) and make it part of regular development practices.
- Educate and train: Provide training to all stakeholders involved in the process to ensure they understand the importance and methods of threat modelling and risk assessment.
- Regularly reassess: Security is not a one-time effort. Regularly reassess threats and risks in response to new vulnerabilities, changes in the system, or emerging threats.
Security Testing
Security testing is a critical component of the software development lifecycle and overall cybersecurity strategy. It involves evaluating the security features of a system to ensure they protect data and maintains functionality as intended. Here’s an overview of the various types of security testing and how they are typically conducted:
a) Vulnerability scanning: Automated tools scan systems, networks, and applications for known vulnerabilities.
b) Penetration testing (Pen Testing): Penetration testing simulates a cyberattack to identify and exploit vulnerabilities in systems, networks, and applications. It is typically performed by ethical hackers who use the same techniques as malicious attackers but do so in a controlled and authorized manner.
c) Security auditing: This is a systematic evaluation of security controls and processes to ensure they are implemented correctly and effectively.
d) Security assessment: A broader evaluation that encompasses vulnerability scanning, penetration testing, security auditing, and risk assessment. It provides a comprehensive picture of the security posture of an organization.
e) Risk assessment: This process involves identifying, quantifying, and prioritizing risks to organizational assets.
f) Ethical hacking: Similar to penetration testing, ethical hacking involves deliberately attacking an organization’s systems to find vulnerabilities from an attacker’s perspective.
g) Code review: Code reviews can be conducted manually or using automated tools and are an essential part of securing the software development process.
h) Configuration management review: Ensuring that systems and applications are configured securely is crucial.
i) Compliance auditing: Verifying that systems and processes comply with relevant security standards and regulations (such as GDPR, HIPAA, PCI DSS, etc.).
j) Red teaming: A multi-layered attack simulation that tests how well an organization’s people, networks, applications, and physical security controls can withstand an attack from a real-life adversary.
k) Social engineering testing: Testing how susceptible an organization’s staff is to social engineering tactics, such as phishing, pretexting, baiting, or tailgating.
l) Posture assessment: Involves analysing and understanding the security condition of computer systems, networks, and other information assets to identify security vulnerabilities.
Figure-6
(Source: https://www.educba.com/security-testing/)